smarter security for your server
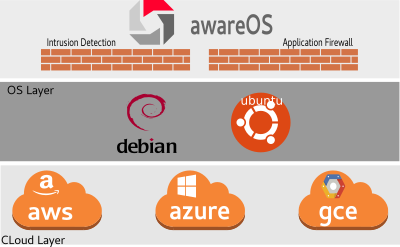
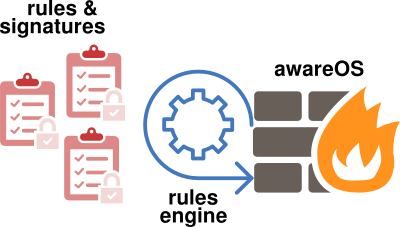
AwareOS is an intrusion detection system (IDS/IPS) that protects your server from network attacks. It does so by analyzing application logs and network traffic in real-time. In contrast to the traditional firewall where rules are statically defined, awareOS dynamically controls them when it detects malicious behavior
Intrusion Detection
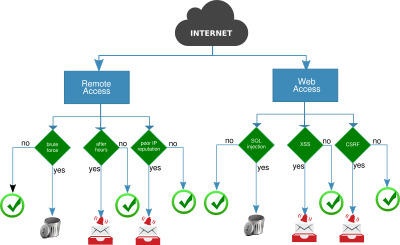
As the threats become more advanced, so have to be the defensive measures on a server. The awareOS product employs both traffic and logs analysis in detecting imminent or ongoing attacks. Whether it is a Slowloris DoS attack designed to exhaust server resources, or brute forcing attempts on the SSH server, this software will provide a wide array of preventive measures against different threat signatures. Your system will be protected 24/7, no human intervention required.
Active Defense
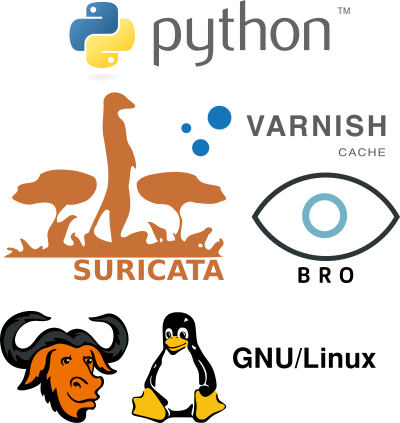
This product stops attacks at the IP layer using the Linux kernel packet filtering facility with dynamically generated rules/tables. In the past, firewall policies were defined once and rarely modified. This approach worked well in in simple web server environments. However, as the organization needs evolve and application become more complex, attack surface of these servers increased. Therefore, we recommend businesses to invest in intrusion detection systems with an active defense mechanism.
Web Application Firewall
Web applications are often the prime target of attacks. Frequently, it is because of an older version of the software where a known vulnerability can be exploited. Therefore, the best form of defense is to keep software up-to-date. In awareOS, we use Varnish, an open source caching HTTP reverse proxy. Not only does it help speed up sites, but also it helps secure web server against DoS and other forms of attacks. Varnish comes with a unique configuration language, VCL. We provide a custom policy that can be used with any application server, such as Apache, NGINX, Tomcat, etc. With the default policy you can, for instance, throttle requests, modify content served by the web server, redirect mobile clients to a different part of the server, etc.
Reports and Alerts
The software can be configured to send alerts when specific events happen. For some services like remote access, it may be important to restrict it after business hours. System alerts are one way to notify a designated person when someone logs in to the server at midnight. Or, when suspicious high volume, unusual DNS names, interesting content transmission, e.g. CC, SSN, traffic is detected. Examples can be numerous. This capability will enable you to receive messages when an network event you subscribe to happens. In addition, a designated business manager, can receive periodic reports on network statistics, security checks performed, highlighting important events.